Market Definition
Zero Trust Security refers to a paradigm of cybersecurity that presupposes no implicit trust on any user, device, or network, both within or outside the perimeter. It has a constant verification of identities and a strict access control with principles of least privilege, real-time monitoring and segmentation. This reduces the attack surfaces and minimizes the movement within the systems laterally, making it more resilient to advanced cyber threats.
The market comprises a variety of integrated cybersecurity solutions like identity and access management (IAM) to regulate user and device authentication, multi-factor authentication (MFA) to enhance identity verification, and micro-segmentation to separate segments of the network and limit access without authorization.
Zero Trust Security Market Overview
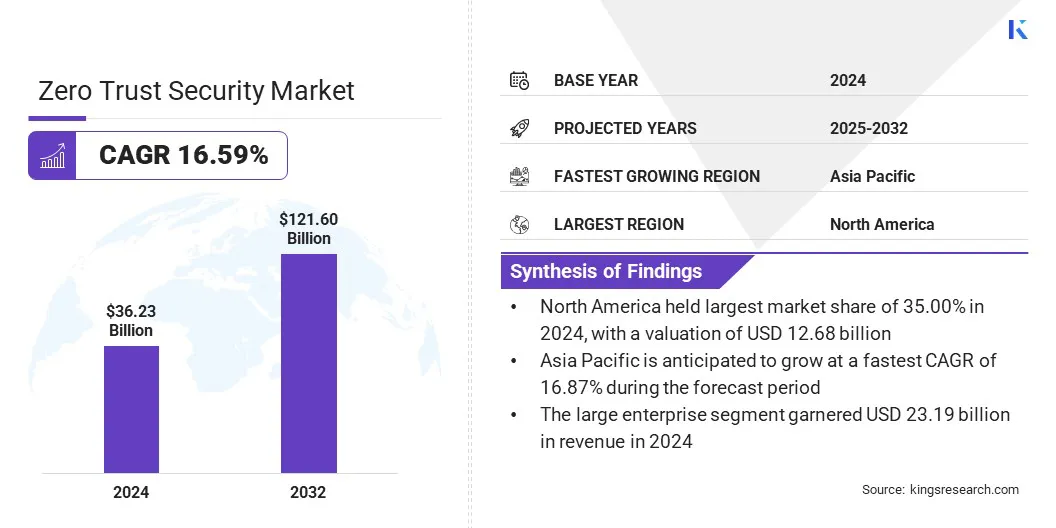
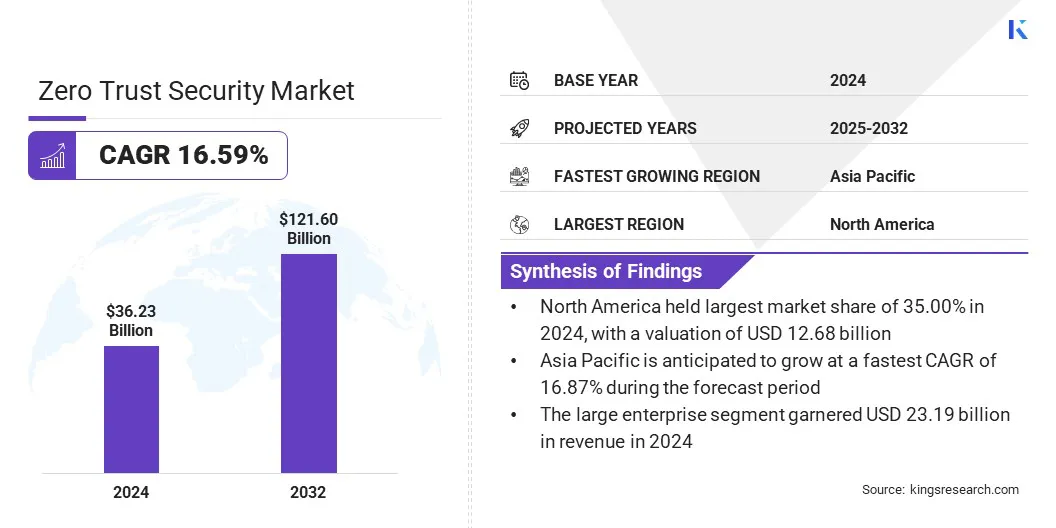
The global zero trust security market size was valued at USD 36.23 billion in 2024 and is projected to grow from USD 41.52 billion in 2025 to USD 121.60 billion by 2032, exhibiting a CAGR of 16.59% during the forecast period.
The market is experiencing a major transformation as organizations are shifting off the old, perimeter-based defenses and adopting a more holistic, identity-based approach. This development is directly connected to the increasing cyber threats, remote working, adoption of cloud technologies, and the burst of IoT devices. All of these factors have broadened the attack surface, making traditional security models less effective.
Major companies operating in the zero trust security industry are Palo Alto Networks, Zscaler, Inc., Cloudflare, Microsoft, Akamai Technologies, CrowdStrike, Cisco Systems, Inc., Netskope, Check Point Software Technologies Ltd., IBM, Delinea, Ivanti, Fortinet, Inc., Broadcom, and Nord Security.
As generative AI becomes more common, organizations are adopting strong security measures to ensure the safe and compliant use of AI technologies. Implementing zero trust architecture offers advanced security features, including real-time AI security posture, dynamic policy enforcement on the network edge, and central monitoring of AI model interactions.
These integrated security layers allow organizations to keep their data secure and compliant, facilitating the confident innovation of AI technology. The increasing advancements in AI technology have led to rapid investment in Zero Trust architecture, making it a necessity for AI security.
- In August 2025, Cloudflare launch Zero Trust platform that allows enterprises to safely create and deploy GenAI applications into operation. It has AI Security Posture Management to identify malicious usage of AI, gateway to implement AI policy on the edge, AI prompt protection to raise red flags in risky interactions among employees with AI, and centralized MCP Server Control to manage called AI tools.
Key Market Highlights
- The zero trust security market size was valued at USD 36.23 billion in 2024.
- The market is projected to grow at a CAGR of 16.59% from 2025 to 2032.
- North America held a market share of 35.00% in 2024, with a valuation of USD 12.68 billion.
- The network security segment garnered USD 11.59 billion in revenue in 2024.
- The cloud based segment is expected to reach USD 77.17 billion by 2032.
- The single factor authentication segment is expected to reach USD 63.41 billion by 2032.
- The large enterprise segment is expected to reach USD 78.79 billion by 2032.
- The BFSI segment is expected to reach USD 42.53 billion by 2032.
- The market in Asia Pacific is anticipated to grow at a CAGR of 16.87% during the forecast period.
How do government regulations and cyber insurance requirements influence the adoption of Zero Trust frameworks?
The increase in regulatory demands and the changing standards in cyber insurance are making zero trust a strategic decision and a non-negotiable operational imperative. In critical infrastructure industries, governments are enforcing stringent micro-segmentation and identity-based access control, making any operational failures in this area tantamount to legal liabilities.
Simultaneously, insurers employ zero trust adoption as a key underwriting criterion, either refusing coverage or imposing elevated premiums on businesses that do not demonstrate comprehensive, explicit oversight of all users and devices. Such regulations create a constant cycle of growth where organizations adopt these frameworks to maintain legal eligibility and financial protection, accelerating market expansion through mandatory compliance.
- In February 2026, Akamai developed a new type of cybersecurity system, which includes Guardicore Segmentation Software and NVIDIA BlueField DPUs. This is a new agentless zero trust solution that delivers real-time segmentation, detection, and isolation of various types of attacks without compromising performance. This helps to avoid regulatory compliance and insurance risks due to the increasing number of cyber-attacks.
Why does continuous monitoring and validation hinder Zero Trust?
Comprehensive user and device verification is a challenge in the zero trust model as it demands a change in mindset from a one-time verification to a continuous model that never assumes trust. But achieving this state is technically challenging because organizations have to monitor various real-time factors like device health, location, and behavioral anomalies in highly distributed environments. In addition, there can be legacy environments that do not have modern API or MFA capabilities. Moreover, security teams have to deal with a friction paradox in which higher verification frequencies can negatively impact the user experience.
To mitigate this challenge of implementing zero trust, organizations are adopting integrated and adaptive security solutions that are equipped with continuous user and device verification and seamless authentication systems. Many organizations are now seeking to integrate their current systems with Zero Trust architectures. The goal is to ensure compliance and facilitate agile threat response, all while keeping productivity and user experience intact.
- In March, 2026, Netskope combined Imprivata Enterprise Access Management and its Zero Trust Engine to improve the security of healthcare. This distribution provides quick, passwordless accessibility, an adaptive, identity aware strategy, and real-time safeguarding of PHI on shared clinical workstations that guarantee regulatory requirements, ransomware threats, and clinical process efficiency.
How is passwordless ZTNA influencing the market?
Zero trust Network Access (ZTNA) passwordless is gaining momentum in the market of zero trust security, as most vendors now seek superior and more convenient ways to authenticate users. This shift has brought an end to the use of traditional passwords which can be easily decrypted by cybercriminals.
It has also provided the use of other forms of more secure authenticators. This passwordless approach applies the fundamental concept of zero trust that requires every user to be continuously authenticated prior to accessing any resource since it requires constant validation instead of a single initial login.
- In February 2026, Portnox expanded its password-less Zero Trust Network Access (ZTNA) to include console-based applications like RDP, SSH, VNC, and Telnet. It provides device monitoring, automated remediation, and unauthenticated, context-sensitive access with no credentials and is seamlessly connected with identity providers, improving user experience and security without VPNs or agents.
Zero Trust Security Market Report Snapshot
|
Segmentation
|
Details
|
|
By Offering
|
Network Security, Data Security, Endpoint Security, Cloud Security, API Security, IoT Security
|
|
By Deployment Mode
|
Cloud Based, On Premise
|
|
By Authentication Type
|
Single Factor Authentication, Multi-Factor Authentication
|
|
By Organization Type
|
Large Enterprise, Small and Medium Enterprise
|
|
By End-user
|
BFSI, IT and Telecommunications, Healthcare, Retail and E-commerce, Utilities, Others
|
|
By Region
|
North America: U.S., Canada, Mexico
|
|
Europe: France, UK, Spain, Germany, Italy, Russia, Rest of Europe
|
|
Asia-Pacific: China, Japan, India, Australia, ASEAN, South Korea, Rest of Asia-Pacific
|
|
Middle East & Africa: Turkey, U.A.E., Saudi Arabia, South Africa, Rest of Middle East & Africa
|
|
South America: Brazil, Argentina, Rest of South America
|
Market Segmentation
- By Offering (Network Security, Data Security, Endpoint Security, Cloud Security, API Security, and IoT Security): The network security segment generated USD 11.59 billion in 2024, driven by its critical role as the primary enforcement layer of Zero Trust. Organizations can dynamically shut the lateral movement by isolating workloads by replacing flat perimeters with micro-segmentation. At the same time, SASE and ZTNA convergence create identity-centric connectivity, which replaces the previous VPNs that supported remote working. These advancements develop the network into a source of real-time telemetry and dynamic policy enforcement, making it the most fundamental component of verifying every digital interaction.
- By Deployment Mode (Cloud Based, On Premise): The cloud-based segment dominated the market with a 62.00% share in 2024. This is due to its ability to support a distributed workforce with superior scalability and real-time identity-based access, which is not possible in legacy on-premise solutions. Cloud-based systems are also efficient in quickly removing any emerging threats. The real-time patching of all zero-day vulnerabilities of endpoints occurs instantaneously and is also assisted by AI-based behavioral analysis.
- By Authentication Type (Single Factor Authentication, Multi-Factor Authentication): The single factor authentication (SFA) segment is projected to reach USD 63.41 billion by 2032. Given that single factor authentication is efficient and can be integrated easily with zero trust models. Although zero trust models place emphasis on continuous verification, many organizations prefer single factor authentication to simplify user access, thereby not compromising their security model. This model is best used in scenarios where the need for rapid deployment and user convenience is critical. Moreover, single factor authentication acts as a foundational layer before the use of more sophisticated authentication models.
- By Organization Type (Large Enterprise, Small and Medium Enterprise): The large enterprise segment is projected to reach USD 78.79 billion by 2032, due to the fact that large organizations invest more in sophisticated zero trust solutions, and has a more complicated IT infrastructure. Large organizations tend to have numerous internal networks, remote offices, cloud environments, and distributed workforces, which leads to a complex infrastructure that cannot be secured using the old methods of security perimeters. Large organizations are better positioned to adopt advanced zero trust systems. These systems use network segmentation to protect against complex, ongoing cyber threats.
- By End-user (BFSI, IT and Telecommunications, Healthcare, Retail and E-commerce, Utilities, and Others): The BFSI segment is projected to reach USD 42.53 billion by 2032, due to the necessity of safeguarding sensitive financial information and adherence to the stringent regulations of the BFSI segment. Its comprehensive digital transformation elevates cybersecurity threats, necessitating regular validation and identity-based controls. Zero trust solutions provide micro-segmentation and least privilege access, thereby reducing risk surfaces and lateral movement. This helps BFSI organizations to securely operate and maintain compliance with regulations.
What is the market scenario in North America and Asia Pacific?
Based on region, the zero trust security market has been classified into North America, Europe, Asia Pacific, Middle East & Africa, and South America.

North America zero trust security market share of 35.00% in 2024 in the global market, with a valuation of USD 12.68 billion. The region has been witnessing growth due to strategic innovation in the form of simplifying the deployment process and increasing the level of automation to improve efficiency in operations.
The major players in the region are moving away from fragmented security systems to unified and cloud-delivered bundles that incorporate adaptive authentication, dark web credential monitoring, and endpoint security into one single interface.
Additionally, advanced real-time intelligence and patch management tools improve incident response efficiency. These strategies are designed for sectors in the region that are tightly regulated, such as finance and government, reinforcing North America’s leadership in delivering scalable, integrated zero trust frameworks.
The Asia Pacific zero trust security industry is expected to register the fastest growth in the market, with a projected CAGR of 16.87% over the forecast period. This growth is sustained by strategic partnerships that bring together superior zero trust security, cellular IoT, and operational technology networks to address critical weaknesses in distributed environments across Southeast Asia.
These partnerships combine expertise in connectivity management and AI-driven threat protection, which is critical for the continuous monitoring and response required for securing growing smart infrastructure. Additionally, there is a large-scale investment driving digital transformation by improving cloud infrastructure, artificial intelligence, and secure hybrid environments.
Both public and private investments are aimed at creating strong cloud services and digital ecosystems that are imperative to the fast development of connected devices and the growth of zero trust schemes in complicated and large-scale settings.
- In March 2026, Zscaler entered into an MoU with Singtel Singapore to provide zero trust security for cellular IoT and OT devices in Southeast Asia. The partnership aids in rapid and scalable security for SIM-connected devices, providing better visibility and minimizing operational risks to ensure a secure digital transformation in mission-critical industries.
Regulatory Frameworks
- In the U.S., federal cybersecurity and defense sector security is governed by the Department of Defense's Zero Trust Reference Architecture and the National Security Agency's Zero Trust Implementation Guidelines. These frameworks and regulations necessitate the adoption of zero trust architectures by defense organizations and federal agencies.
- In the European Union, the General Data Protection Regulation is the regulatory framework that provides guidelines on data privacy and protection. This regulation is in compliance with the Zero Trust model, which ensures that data protection measures are implemented and designed by default, thus providing the security required to access personal data only when needed.
Competitive Landscape
Key players are shifting from isolated security tools towards unified platforms that incorporate identity, device intelligence, and cloud access. Companies have also focused on AI-driven automation as a way to deliver proactive threat detection and remediation, which will ultimately reduce the overall IT workload.
There has been a major focus placed on the critical infrastructure's security, with providers using agentless and hardware-accelerated solutions to protect legacy infrastructure without impacting performance. The market has also witnessed the rise of Gen AI governance, with many tools monitoring AI engagements. By providing these services as simple packages, the companies have made them scalable for diverse industries.
- In March 2026, Netskope and Forescout partnered to give a Zero Trust solution combining Forescout’s device intelligence into Netskope’s AI-based cloud security. This solution secures IT, IoT, and IoMT devices with regular risk assessment, traffic control, and support for compliance.
Key Companies in Zero Trust Security Market:
- Palo Alto Networks
- Zscaler, Inc.
- Cloudflare, Inc.
- Microsoft
- Akamai Technologies
- CrowdStrike
- Cisco Systems, Inc.
- Netskope
- Check Point Software Technologies Ltd.
- IBM
- Delinea
- Ivanti
- Fortinet, Inc.
- Broadcom
- Nord Security
Recent Developments (Partnerships/Agreements/ Product Launch)
- In March 2026, Tata Consultancy Services extended its collaboration with Zscaler to launch TCS Workspace Experience Studio, which was built with Zscaler Digital Experience (ZDX). The AI-driven solution also includes zero trust security, powerful digital experience monitoring, and auto-remediation to improve productivity by 25-30% and improve user experience, as well as facilitate proactive IT functions.
- In December 2025, WatchGuard introduced WatchGuard Zero Trust Bundle, unifying adaptive MFA, SSO, Dark Web Credential Monitoring, EPDR, and FireCloud Total Access into a single cloud-delivered platform. Making implementation of zero trust easier for organizations and MSPs and offers uninterrupted device validation, risk-based access, and automatic threat containment without VPN complexity.
- In December 2025, Xage Security and LTIMindtree formed a strategic partnership to provide scalable Zero Trust cybersecurity to the most vulnerable critical infrastructure sectors of energy, utilities, and transportation. Combining Xage Fabric's identity-based access and AI-driven protection with LTIMindtree's global expertise, they enable secure IT, OT, and cloud convergence with simplified management and rapid deployment.
- In October 2025, Siemens released SINEC Secure Connect, which virtualizes network structures via overlay networks. It provides protection of Machine-to-Machine, cloud, datacenter without VPN, unauthorized access, simplified management, on-premises and cloud-based applications, and integrates with Siemens SCALANCE equipment.